This is an old revision of the document!
Group Managed Service Accounts
Security information
This tutorial only shows the general procedure. Depending on the company structure, an appropriate authorisation concept must be planned in advance. Important questions that should be clarified in advance:
- How should authorisations be assigned (group authorisations, individual authorisations)?
- How do we structure our gMSA accounts (per server, per service, etc.)?
Preparations
Create root key on the DC:
Add-KdsRootKey -EffectiveImmediately
Then wait 10 hours to ensure that the replication is complete.
gMSA account
Create
On the DC:
New-ADServiceAccount -Name <ACCOUNTNAME> -DNSHostName <ACCOUNTNAME>.<DOMAIN>.<TLD> -PrincipalsAllowedToRetrieveManagedPassword <COMPUTERNAME>$
test
On the target system:
Test-ADServiceAccount <ACCOUNTNAME>
If successful, the console reports True
For errors on the target system
The RSAT tools may need to be activated. Statement from Microsoft on this:
As of the Windows 10 October 2018 Update, RSAT is included as a collection of features on demand in Windows 10 itself. Instead of downloading an RSAT package, you can now simply navigate to Manage optional features under Settings and click Add feature to see the list of available RSAT tools. Select the desired RSAT tools and install them. To view the installation progress, click the Back button to view the status on the Manage Optional Features page.
https://learn.microsoft.com/de-de/windows-server/remote/remote-server-administration-tools
If the Powershell is still open, you can also start the installation with this command:
Install-WindowsFeature -IncludeAllSubFeature RSAT
After the installation, a restart may be required and the ActiveDirectory module must be imported into PowerShell:
import-module ActiveDirectory
Authorisations
The authorisations can now be assigned as required. Either by assigning a security group in AD or as a local administrator on the target system. Authorisation concepts should only ever contain the authorisations that are really necessary.
Services
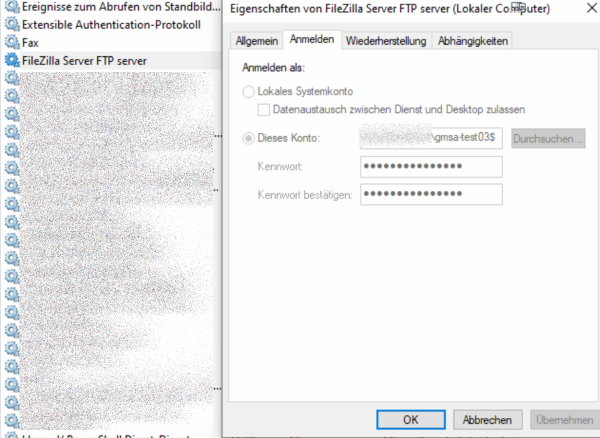
Services can now be started in this user context. To do this, simply open the service console and navigate to the properties of the service:
Log inOpen tab- Select
This account <ACCOUNTNAME>from the domainPasswordEmpty fields- Confirm dialogue
Task planning
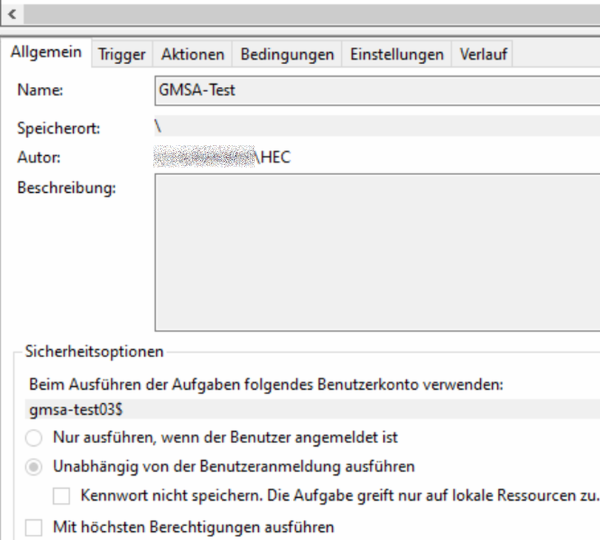
To execute a task in the context of the gMSA account, this task must be customised using the command line
schtasks /Change /TN "<AUFGABENNAME>" /RU "<DOMAIN>.<TLD>\<ACCOUNTNAME>$" /RP ""
The account may need to be granted the right to log in as a batch processing task:
Sources: